The Challenge of Origins
Your banking dashboard lives at https://mybank.com , but the stock market widget is hosted at https://stockmarket.com. You decide to embed their widget using an iframe:
<!-- On your banking dashboard -->
<iframe src="https://stockmarket.com/widget"></iframe>But then you realize: the widget needs to know the user’s investment preferences stored in your application, and your application needs to know when the user interacts with the widget. So you try to approach:
// Trying to directly access the iframe's content
const widgetFrame = document.querySelector('iframe');
try {
widgetFrame.contentWindow.updatePreferences({
stocks: ['AAPL', 'GOOGL']
});
} catch (error) {
console.error(`Oops! This doesn't work!`);
}🚫 Error : “SecurityError: Blocked cross-origin access”
Understanding the Security Barrier
This is where you encounter the “Same-Origin Policy” – a fundamental security feature of web browsers. But first let me explain it to you that what an origin is:
An origin is defined by three components:
What is an Origin?
- Protocol (e.g., http:// or https://)
- Domain (e.g., example.com)
- Port (e.g., :80, :443)
For example:
https://example.com:443
└─┬──┘ └───┬────┘ └─┬─┘
│ │ │
Protocol Domain PortSame-Origin Policy
Browsers implement a security measure called the “Same-Origin Policy” which:
- Restricts how documents/scripts from one origin can interact with resources from another origin
- Prevents malicious sites from reading sensitive data from another site
- Is a fundamental security mechanism in web browsers
so by saying so, origins that are not the same cannot access or manipulate each other’s data directly, ensuring that sensitive information is protected and preventing unauthorized cross-origin interactions.
Examples of different origins:
// These are different origins:
https://example.com
http://example.com // Different protocol
https://api.example.com // Different subdomain
https://example.com:8080 // Different port
https://other-site.com // Different domain
// These are same origin
// the path is excluded, only the 1st 3 parts are important:
// Protocol , Domain, Port):
https://example.com/page1
https://example.com/page2
https://example.com/api/dataSo in our example lets consider some related examples of the same & different origins:
- Same Origin (✅ Allowed):
Your pages:
- https://mybank.com/dashboard
- https://mybank.com/settings
- https://mybank.com/profilethey’re from the same building.
- Different Origin (❌ Blocked):
Your page: https://mybank.com
Widget page: https://stockmarket.comThese can’t directly communicate with each other.
But what now? How are we supposed to communicate with a 3rd party widget (with a different origin)?
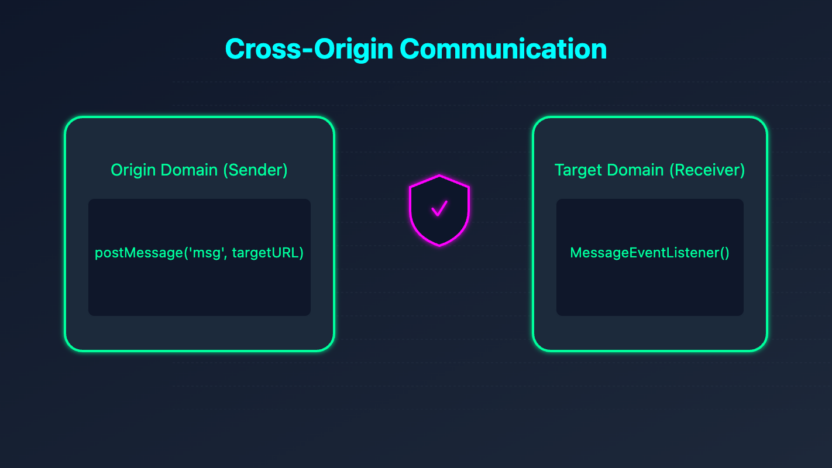
postMessage: The Secure Messenger
This is where postMessage comes in. It’s a method that enables secure communication between different origins by passing messages between Windows, iframes, or Web Workers. It was introduced to allow controlled communication across domain boundaries while preventing malicious cross-site scripting attacks.
You might wonder, ‘Is it really possible to communicate with a different origin? And if we have such a solution, can we communicate with any origin different from our own? What about security concerns?’
The answer is yes – postMessage provides a secure way for two different origins to communicate and exchange data, but with important safeguards in place. However, this communication isn’t unrestricted or universal. You can’t simply communicate with any origin you want; it follows a structured protocol where:
- The sender (Parent Window: your origin) must format and send the data in a specific way
- The receiver (Child Window: the different origin, such as an iframe embedded in your page) must explicitly listen (eventListener) for these messages
- Both parties need to agree on this communication channel and implement proper security checks
Think of it like a secure diplomatic channel: messages can only be exchanged when both parties are prepared and following the proper protocols. The receiver must have an event listener for ‘message’ events ready to capture and process data from your origin, while the sender must properly structure and direct their messages to the intended recipient.
postMessage Syntax & Code Example
Basic Syntax
targetWindow.postMessage(message, targetOrigin, [transfer]);- targetWindow: The window object receiving the message
message: The data to send (can be any serializable value)targetOrigin: Specifies which origin can receive the messagetransfer: Optional array of transferable objects
Code Example
Parent Window (sender, your origin: https://mybank.com):
// On your banking dashboard (sender)
const message = {
type: 'UPDATE_PREFERENCES',
stocks: ['AAPL', 'GOOGL']
};
// Send message to specific address only
widgetFrame.contentWindow.postMessage(message, 'https://stockmarket.com');Child Window (receiver, the different origin, the iframe’s origin: https://stockmarket.com):
// In the widget (receiver)
window.addEventListener('message', (event) => {
// Check the sender's ID (origin)
if (event.origin !== 'https://mybank.com') {
return; // Reject messages from unknown senders
}
// Process the message
console.log('Received preferences:', event.data);
});Why postMessage is Special
- Security with Control
// You can specify exactly who can receive the message
postMessage(data, 'https://stockmarket.com'); // ✅ Specific target
postMessage(data, '*'); // ⚠️ Anyone can receive2. Origin Verification
// Receiver can verify sender's identity
window.addEventListener('message', (event) => {
const trustedSenders = ['https://mybank.com', 'https://bank-api.com'];
if (!trustedSenders.includes(event.origin)) {
return; // Reject untrusted senders
}
// Process message...
});3. Structured Communication
// Send organized, typed messages
postMessage({
type: 'USER_ACTION',
action: 'BUY_STOCK',
data: {
symbol: 'AAPL',
quantity: 10
}
}, targetOrigin);Common Use Cases
- Cross-Origin API Requests
- Shared Authentication
- Real-time Data Updates
- Feature Coordination
- Cross-Window State Management
Browser Support and Limitations
postMessageis supported in all modern browsers- Messages must be serializable (can’t send functions or DOM nodes)
- Performance may be impacted when sending large amounts of data
- Some browsers limit the size of messages
Conclusion
postMessage provides a secure and reliable way to implement cross-origin communication in web applications. By following security best practices and implementing proper message validation, you can create robust communication channels between different origins while maintaining security.